Products and Applications
IP Intercoms and IP Access Control
 Our IP-based devices are key components in door entry and door access control systems. How do we focus on cybersecurity?
Our IP-based devices are key components in door entry and door access control systems. How do we focus on cybersecurity?
Physical Security
We mostly install intercoms outside buildings. Access units are more suitable for indoor use, but a lot of random visitors may use them during the day. The first step in cybersecurity is the physical security of our products.
- Anti-vandal – products available in robust materials, such as aluminium or zinc alloy with IP69K and IK10.
- Built in mechanical or optical tamper switch – unauthorized intrusion triggers sensors which activate alarms or send emails with several snapshots.
- Security relay – enhances door entry security by preventing tampering with the intercom and the opening of locks by force. Install it between the intercom and the lock.
Network Security
Secure communication is the backbone of every household or company. We strive to protect customer data with built-in functions and protocols in our devices.
- HTTPS – data encryption protects the connection between web browsers and web servers in 2N devices from unauthorised access and falsified data.
- IEEE 802.1x – establishes a point-to-point connection and prevents access from the LAN port if authentication fails, thereby preventing port hijacking.
- SIPS – protocol encrypts the content of SIP messages, preventing the misuse of data (man-in-the-middle attack) and identity theft.
- SRTP – protocol encrypts voice data, preventing unauthorised persons from listening in to any communication.
Intelligent Password System
To increase site security, use a strong password and do not share it with anyone. 2N will help you create such a password.
- Weak password control – a function that checks whether an administrator has changed a password after the first login. It also checks whether the password is weak.
- Encrypted password – passwords are saved in encrypted form, preventing hackers from gaining login data from the configuration.
Secured Readers
- The transition from obsolete, easily copied technology to much securer technology has arrived! 2N access units read PACs ID (HID iClass cards with an SIO object).
Indoor Stations
 Answering units are an indispensable part of door communication, which is why they must meet robust security requirements.
Answering units are an indispensable part of door communication, which is why they must meet robust security requirements.
2N OS Indoor Stations: 2N® Indoor View, 2N® Indoor Compact and 2N® Indoor Talk
- You’ve already learned about network security for 2N intercoms (HTTPS, SIPS, etc.). That is the reason communication between 2N intercoms and 2N Indoor Stations is secured.
- After the first login, users are immediately prompted to change the default password to a strong password.
Android Indoor Station: 2N® Indoor Touch 2.0
- HTTPS – used in products with 2N OS, this protocol is also applied to our Android based products.
- TLS 1.2 – encrypted and secure communication between 2N® Indoor Touch 2.0 and My2N cloud.
- Account policies – different permission levels restrict who can change key security settings. User access privileges are limited only to necessary changes in settings. Administrator rights are extended.
- Encrypted discovery protocol – encrypted network protocol for advertising and network discovery services.
- Access to web API – protected by an administrator password.
Android/iOS Indoor Station: 2N® Mobile Video
- A part of the secure My2N cloud platform.
- Up to date versions of Android and iOS – only the latest versions of iOS and Android are supported. This ensures the latest security updates are installed (iOS 12 or newer, Android 6 or newer).
2N® Mobile Key and Bluetooth Readers (Mobile Phone Access Control)
 The 2N® Mobile Key app and our Bluetooth readers allow users to enter buildings using only their mobile phone. This means mobile credentials should be secure from misuse.
The 2N® Mobile Key app and our Bluetooth readers allow users to enter buildings using only their mobile phone. This means mobile credentials should be secure from misuse.
- Government-grade encryption – Bluetooth communication via our own secure channel using RSA-1024 for key exchange and AES-128 for subsequent communication.
- The validity duration of the initial pairing code can be set by the system administrator, starting from just 10 minutes.
- Maximum distance range setting for Bluetooth communication with devices, starting from 50 cm.
- Multi-factor authentication – users can be required to combine their Bluetooth credentials with other types of credentials, such as an RFID card or a PIN code via an in-app keypad.
- If a smartphone is lost, administrators can quickly delete access rights using the reader’s web interface or 2N® Access Commander. Both are encrypted.
The My2N Management Platform
My2N is a reliable cloud platform that allows administrators to remotely manage installations, products and services, saving their maintenance and travel costs. The My2N platform provides services that require multiple communication interfaces between My2N cloud components and 2N devices. All are described in the following scheme.
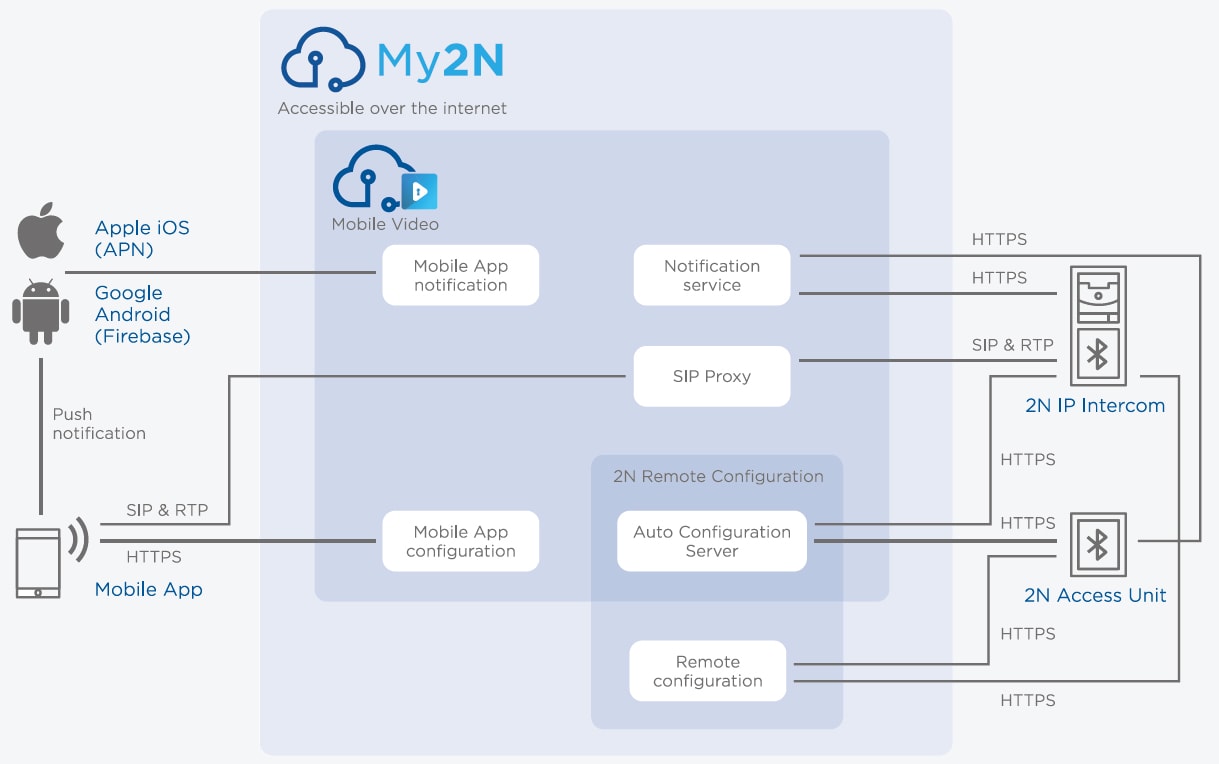
For more information, visit the My2N security page.
2N® Access Commander
2N® Access Commander is professional IP door entry software. It is designed to protect buildings and the people who live and work inside them. The software natively includes functionalities such as visitor management, lift access control, camera logs, anti-passback and open REST API.
- Runs on a secure Debian distribution of Linux, with the Apache web server, and is built on .NET technology.
- HTTPS is used for secure communication between the server and the client.
- The same encryption level using TLS 1.2 is also used for communication between the server and connected devices (2N IP intercoms and Access Units) as well as other features in 2N® Access Commander (emails, LDAP sync or REST API communication).
- Several user roles are available, allowing users’ rights to be limited only to certain tasks, reflecting their role.
- After the first login, the administrator is immediately prompted to change the default password to a strong password.
- The administrator may define their own retention policies for different kinds of logs. Logs outside of these retention policies are not kept.
- Provides a facility to bulk update the firmware of connected devices, helping to ensure that they benefit from the latest updates with the highest possible security.