The Battle for Entry: Which is the Best Door Access Control Technology?
 Marek Chládek, 21. 02. 2023 | 6 min read
Marek Chládek, 21. 02. 2023 | 6 min read
Are you working on a new access control project and wondering what technology to choose? There are essentially six options, each with its own benefits and downfalls.
Let’s go through them:
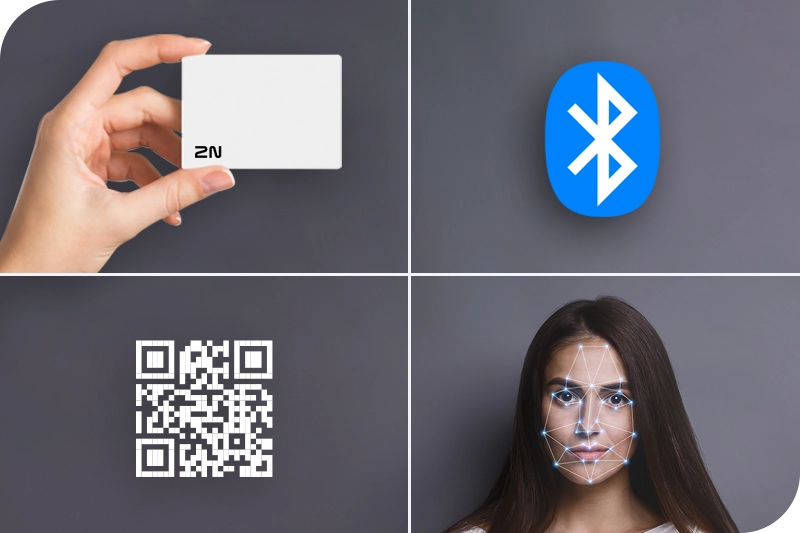
1. Good old RFID
A well-established and still extremely popular technology for IP door access control systems. It will be some time before plastic cards and key fobs are dethroned as the most popular option out there.
On the plus side, they are relatively cheap and reliable and are already being used by millions of people around the world.
On the less positive side, they are easy to lose, and new cards can only be distributed to users in person. They can also be expensive to distribute – and the cheaper types of RFID cards (125 kHz) are very easy to counterfeit. If you want to use RFID technology in your next project, make sure you choose secured RFID cards which, although more expensive, are harder to replicate.
2. PIN
The PIN hasn’t been thrown into the dustbin of history just yet, but it’s certainly past its heyday. Today, it’s most commonly used as a backup method of access control, or as a confirmation method in two-factor authentication (i.e., RFID + PIN).
Recently, it has also been widely used for one-time or time-limited access, supported by the fact that it can also be easily distributed by email or SMS: this provides a convenient way for authorised non-residents (such as cleaners, couriers, or other visitors) to access buildings without keys.
However, there are security concerns with PIN codes – they’re easy to pass on to non-authorised people, and it’s very difficult to verify a user at the point of entry.
3. Fingerprint
Fingerprint access control appears to be the most secure, convenient access control method because users don’t have to carry anything with them and of course – it’s very hard to counterfeit a fingerprint.
Ideal, right? Unfortunately, not quite. The issue with any biometric access method is that you’re storing very sensitive information about users, which can become very complex from a regulatory perspective – particularly in Europe. Thanks to the General Data Protection Regulation (GDPR), the processing of biometric data for the purpose of uniquely identifying people is strictly prohibited. This is a complex and contested area, but regulators in some countries have made it almost impossible to use fingerprint access control in workplaces: so it’s best to think of other options.
 Stay up-to-date with the latest news. Subscribe to our newsletter.
Stay up-to-date with the latest news. Subscribe to our newsletter.
4. Facial recognition
Popularised by smartphone technology, facial recognition is perhaps the most convenient method of unlocking a door. The user simply approaches, the camera recognises their face, and they’re let in.
However, the regulatory issues mentioned about fingerprint access control are an even more serious problem for facial recognition technology, with people in Europe having the right for their personally identifiable information to be deleted or ‘forgotten’.
Moreover, although the technology is improving, facial recognition systems can still be unreliable. Often a photo of an authorised person is enough to fool them. Some facial recognition technologies have also demonstrated identification bias around race and gender, and others have a problem with people wearing glasses.
As a result, if you choose this access method, it will be important to give reviews and testing a higher priority than you might normally.
5. QR codes
QR codes are a modern access control method which is on the rise. Indeed, last year, the 2N OS 2.34 gave the 2N® IP Style intercom the ability to read QR codes.
QR codes are becoming popular for various reasons, not least because of the rise in e-commerce and the growth of flexible working models. Similar to PIN codes, QR codes are easy to distribute to those who require one-off or time-limited access – say for couriers, cleaners, contractors and staff who only need to access the building once (or at certain times/days only).
Conversely to PIN codes (that can be communicated by word of mouth alone), the security level of QR codes is very high. The video intercom 2N® IP Style, for example, supports QR codes that contain 10-15 digits. Cracking a QR code like this would – if you had a lot of time on your hands – theoretically take 115,740 days!
The downside of QR codes is that they are not very suitable for long-term access. They are also not the most convenient option out there because each time you enter the building, you need to find your phone and the QR code stored in it. An alternative is to print the QR code, but that obviously significantly reduces the security of this method.
6. Bluetooth/mobile access control
Mobile phone access control is the fastest-growing form of access control, primarily because it is so convenient.
It’s also flexible because there are many modes of mobile phone access control available: from pressing a button in the app, to putting your phone on the reader, to simply touching the reader and leaving your phone in your pocket. You can even simulate face recognition mode: the camera captures motion and, based on that, the reader starts the authentication process and locates the authorised smartphone; if it finds it and detects it approaching, it will open the door.
But is Bluetooth secure?
Users guard their phones more closely than access cards and are less likely to lose or forget them, so this is an obvious security benefit compared to RFID. In terms of technology, some of the early mobile access control systems had issues with unwanted door opening, but WaveKey (2N’s cutting-edge Bluetooth-based mobile credential access control technology), for example, has an intelligent algorithm which completely eliminates this risk.
It’s a new technology – does that make it expensive?
Not anymore. In fact, mobile access control can be pretty cheap if you can find a company that provides Bluetooth access credentials for free. The more expensive purchase cost of a Bluetooth-enabled reader is then easily offset by the savings on plastic cards. Distribution and pairing are also very simple.
Are there any downsides to mobile credentials?
Probably only one: the user has to have an app, which is no problem for employees or homeowners who need access regularly, but is less suitable for one-time access. This is one of the main reasons that 2N updated its operating system to ensure that the video intercom 2N® IP Style can read QR codes as well as supporting WaveKey – because it means that customers can have the best of both worlds.
Conclusion
So, which is the best option?
We believe that, for most projects, the ideal combination is Bluetooth technology for those who are accessing the building regularly, and QR codes for one-off/time-limited access. However, as always, it will depend on the type of project and the customer’s exact requirements.
Still not sure which access method would be the best fit for your project? Please get in touch - our sales team have huge experience and are always on hand to help.